Inside a Mustang Panda Campaign Targeting European Diplomatic Entities

 A campaign targeting European diplomatic entities was identified during February 2026, affecting organizations in several countries including Italy, Latvia, and France.The attack chain begins with the download of a ZIP archive from a remote URL, most likely delivered through a phishing email. Inside the archive, the initial stage consists of a malicious LNK file themed around BRICS-related information to lure the victim.When executed, the LNK file triggers a sequence of actions that ultimately leads to the side-loading of a malicious DLL using a legitimate Steam executable.
A campaign targeting European diplomatic entities was identified during February 2026, affecting organizations in several countries including Italy, Latvia, and France.The attack chain begins with the download of a ZIP archive from a remote URL, most likely delivered through a phishing email. Inside the archive, the initial stage consists of a malicious LNK file themed around BRICS-related information to lure the victim.When executed, the LNK file triggers a sequence of actions that ultimately leads to the side-loading of a malicious DLL using a legitimate Steam executable.

 Agent Tesla is a Remote Access Trojan (RAT) focused on credential theft. In this analysis, we dissect a .NET sample examining its dynamic in-memory loading capabilities that bypass disk writes, obfuscation techniques employing unconventional naming conventions for variables and functions, and ultimately, the stolen data exfiltrated from the compromised system.
Agent Tesla is a Remote Access Trojan (RAT) focused on credential theft. In this analysis, we dissect a .NET sample examining its dynamic in-memory loading capabilities that bypass disk writes, obfuscation techniques employing unconventional naming conventions for variables and functions, and ultimately, the stolen data exfiltrated from the compromised system.

 This Custom Sample 1 will be divided into several phases, each designed to demonstrate key concepts and techniques used for code obfuscation and evasion of analysis. Throughout these phases, we will explain the step-by-step process of implementing various obfuscation strategies aimed at protecting the integrity of the code while making it harder to reverse-engineer or analyze. Additionally, we will cover the different methods used to avoid detection and analysis by automated systems, showcasing how these techniques are employed to ensure security and confidentiality. Each phase will provide a deeper understanding of the tools and approaches used in the creation of robust, secure systems.
This Custom Sample 1 will be divided into several phases, each designed to demonstrate key concepts and techniques used for code obfuscation and evasion of analysis. Throughout these phases, we will explain the step-by-step process of implementing various obfuscation strategies aimed at protecting the integrity of the code while making it harder to reverse-engineer or analyze. Additionally, we will cover the different methods used to avoid detection and analysis by automated systems, showcasing how these techniques are employed to ensure security and confidentiality. Each phase will provide a deeper understanding of the tools and approaches used in the creation of robust, secure systems.

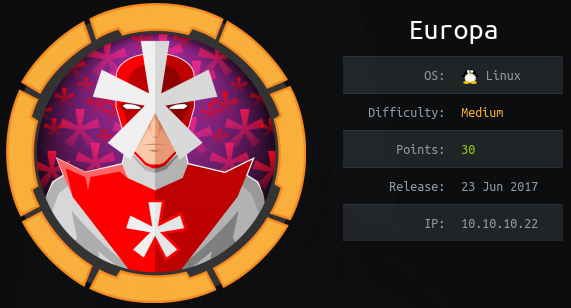 Europa is a medium-friendly difficulty machine on HackTheBox, offers a diverse range of topics that can pose both a challenge and an opportunity for learning. While it doesn’t require an extensive number of steps, it provides a rich learning experience in various aspects of enumeration and attack vectors. Our journey starts with enumeration, where careful attention to certificates will enable us to apply virtualization. Next, we’ll encounter SQL Injection and rejex injection challenges. Finally, the grand finale awaits with a privilege escalation, where we’ll dive into modifying cron task code.
Europa is a medium-friendly difficulty machine on HackTheBox, offers a diverse range of topics that can pose both a challenge and an opportunity for learning. While it doesn’t require an extensive number of steps, it provides a rich learning experience in various aspects of enumeration and attack vectors. Our journey starts with enumeration, where careful attention to certificates will enable us to apply virtualization. Next, we’ll encounter SQL Injection and rejex injection challenges. Finally, the grand finale awaits with a privilege escalation, where we’ll dive into modifying cron task code.
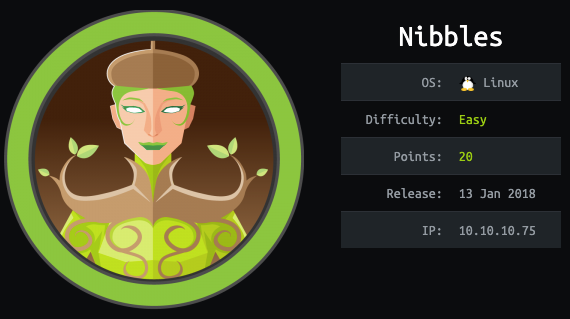 Nibbles is a begginer-friendly machine on HackTheBox, designed to provide an excellent entry point for those new to ethical hacking and penetration testing. It offers a realistic environment to practise skills and tackle challenges in a controlled setting. As you explore and conquer its challenges, you’ll develop essential skills and gain a deeper understanding of penetration testing techniques. In this machine we do enumeration, web application testing, exploitation, privilege escalation and capture the flag.
Nibbles is a begginer-friendly machine on HackTheBox, designed to provide an excellent entry point for those new to ethical hacking and penetration testing. It offers a realistic environment to practise skills and tackle challenges in a controlled setting. As you explore and conquer its challenges, you’ll develop essential skills and gain a deeper understanding of penetration testing techniques. In this machine we do enumeration, web application testing, exploitation, privilege escalation and capture the flag.